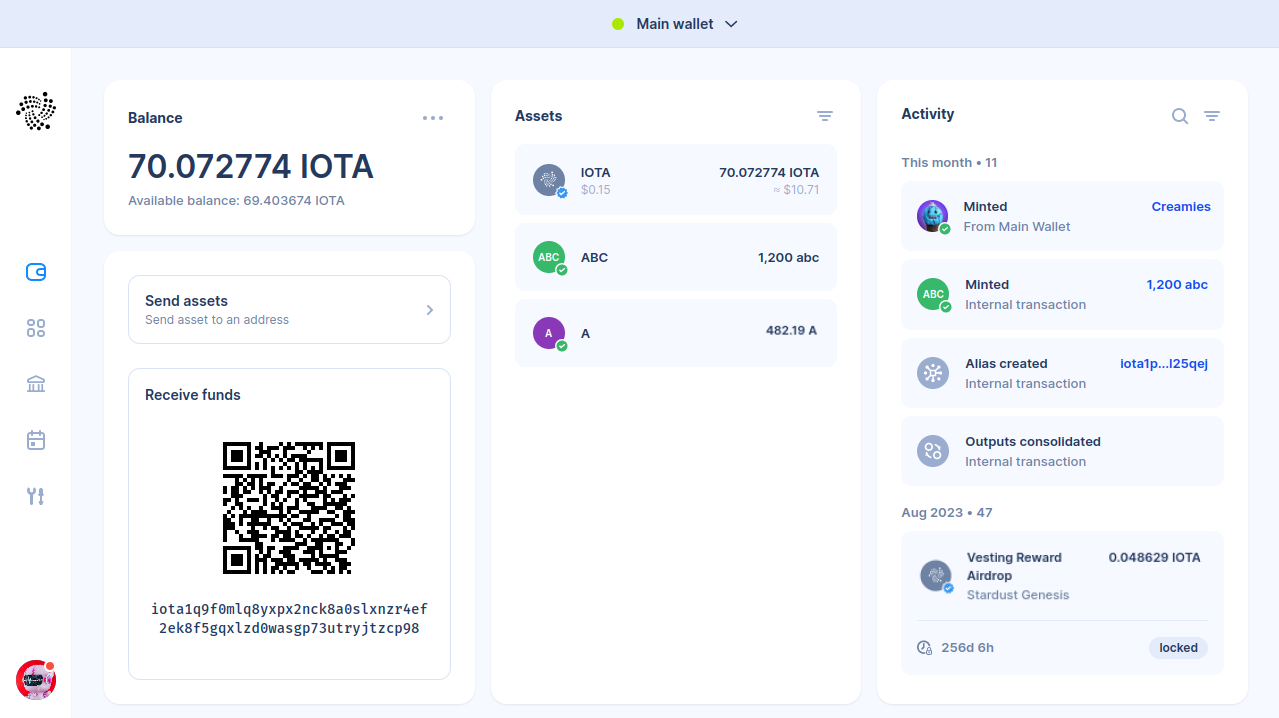
The new Firefly IOTA version compatible with the Stardust network upgrade has been released, introducing new features like native tokens and NFTs. Try it out here.
The Secure Entrypoint to the IOTA Ecosystem.
Download Firefly
Firefly IOTA
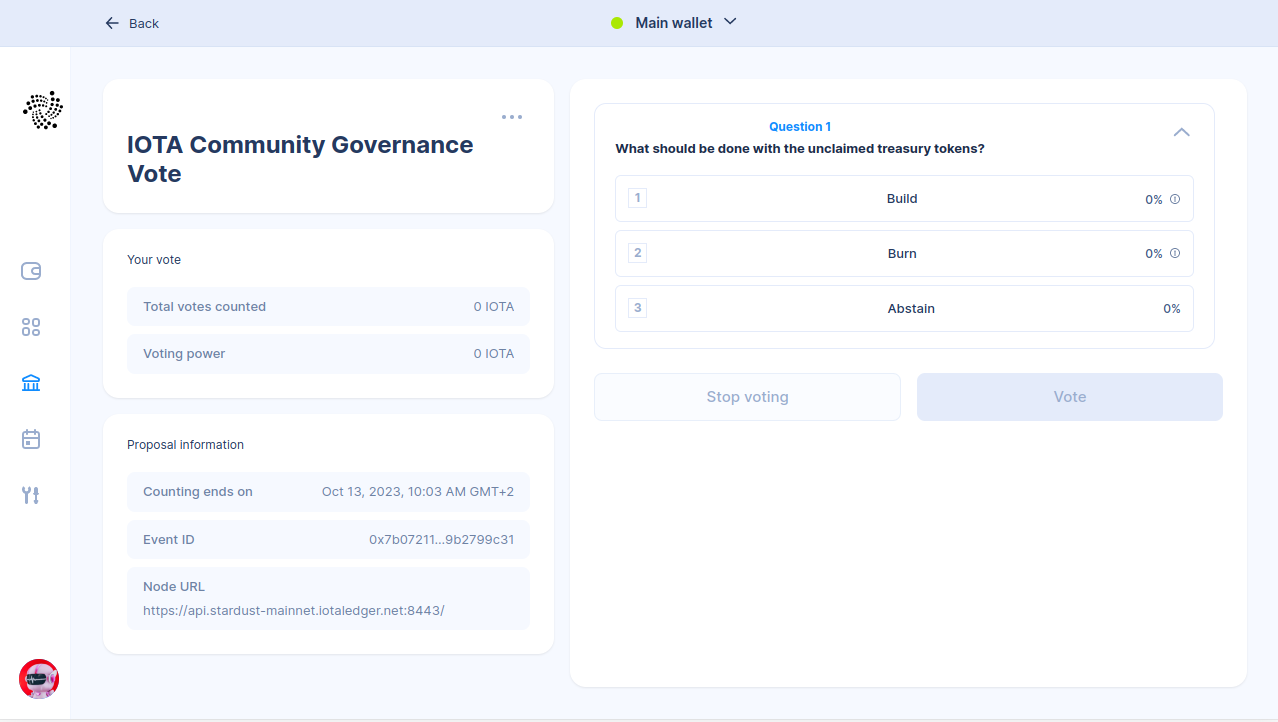
Manage your IOTA assets directly from your computer with both software and hardware wallet support. Earn staking rewards and participate in governance votes.
Firefly Shimmer
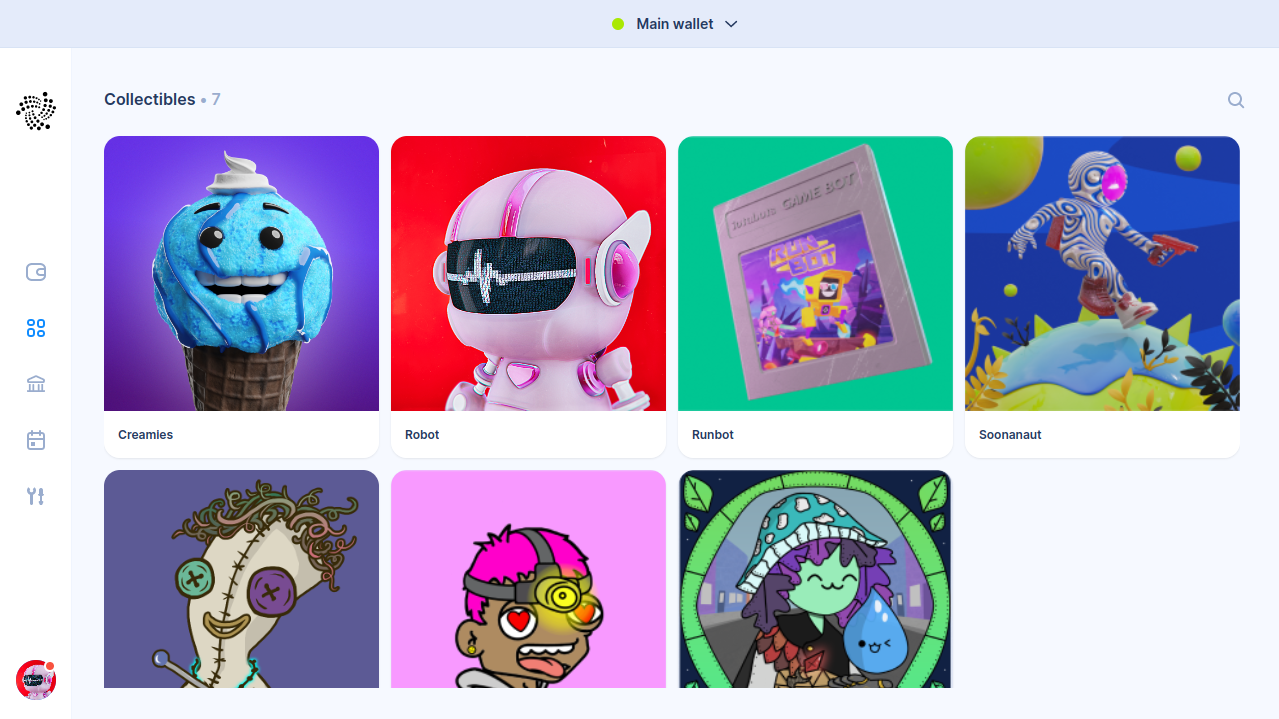
Try out new features introduced with Shimmer, such as minting native tokens, setting transaction expiry times, and sending microtransactions.
A new evolution
Bringing the benefits of Chrysalis
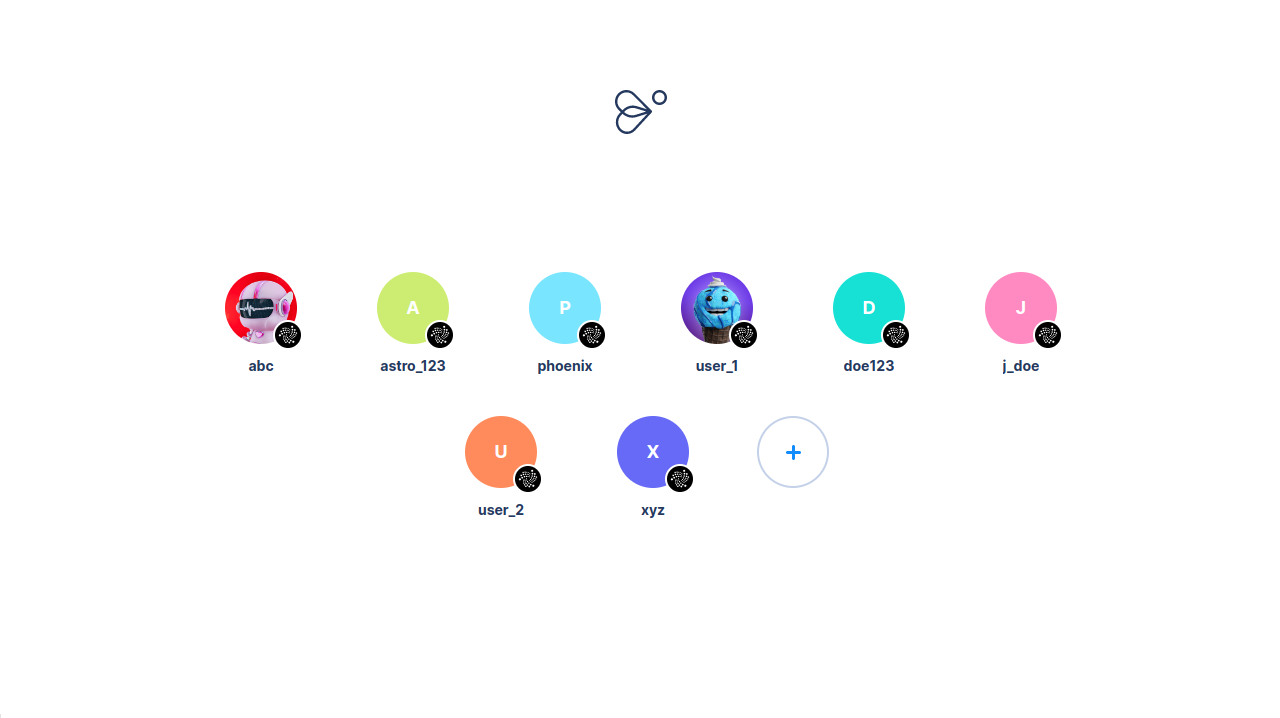
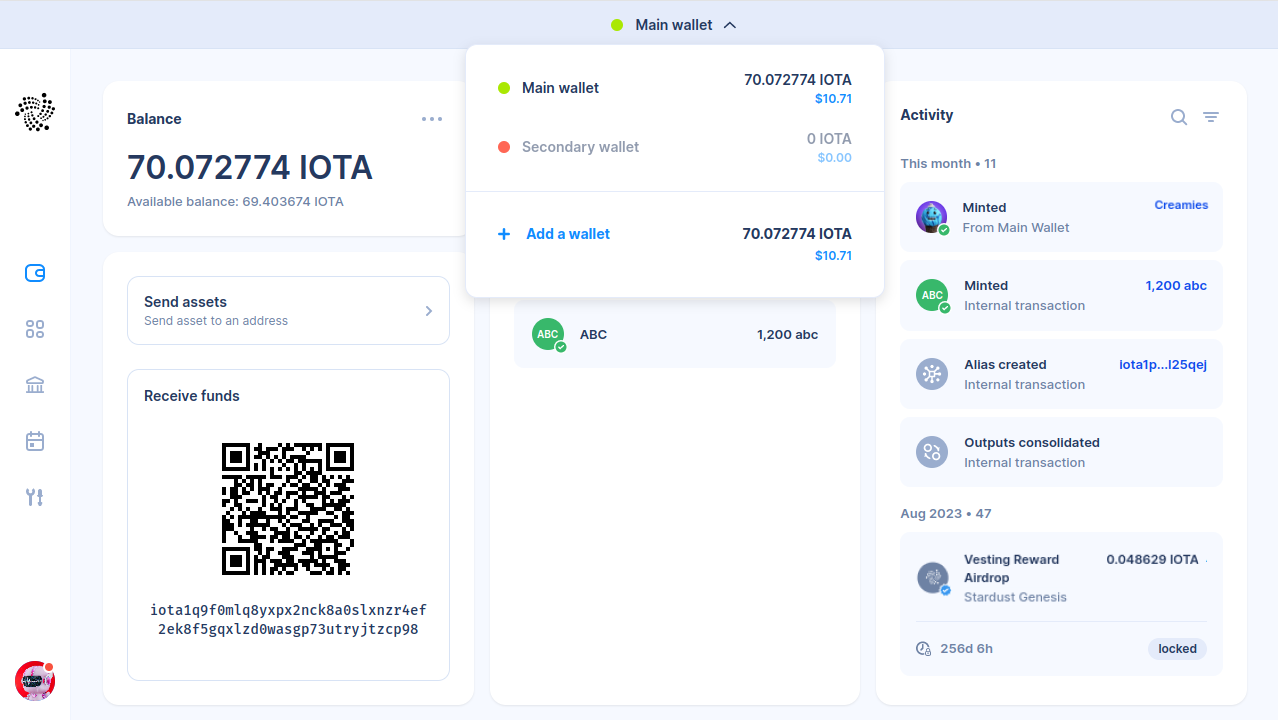
Multiple Wallets
With wallets you can separate your funds across – for example – a main account, a spending account and a Ledger Nano account.
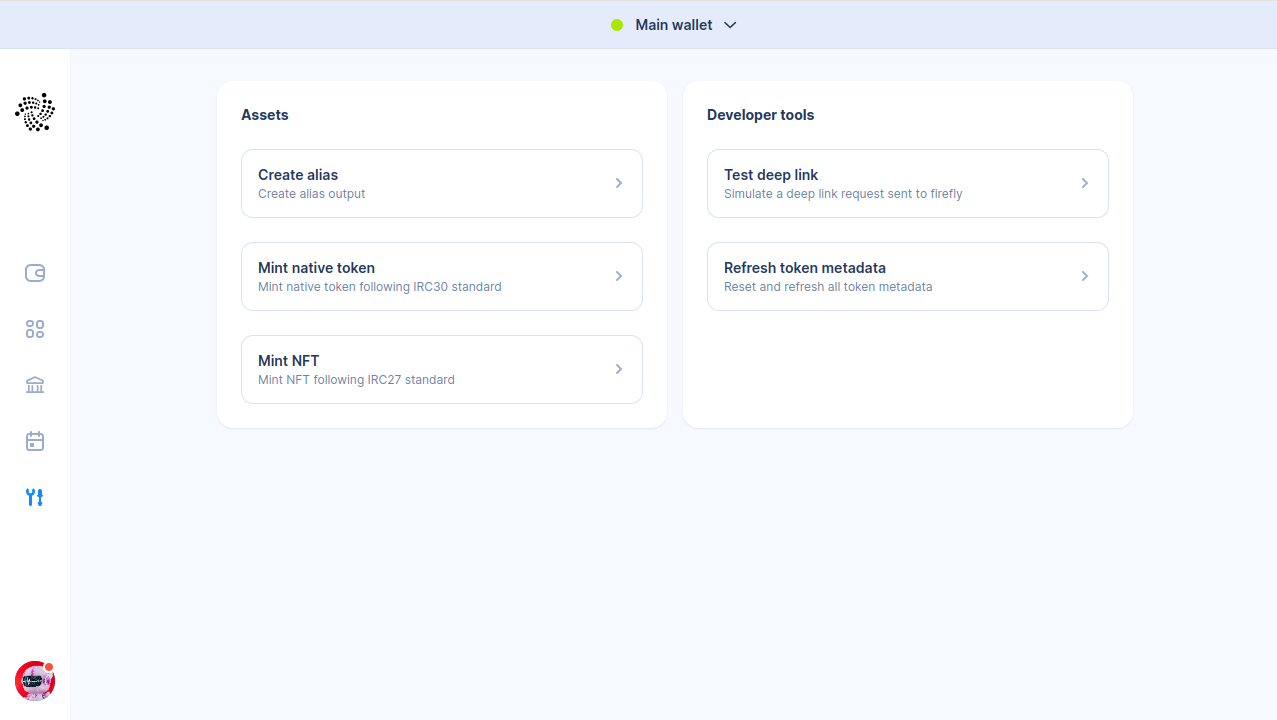
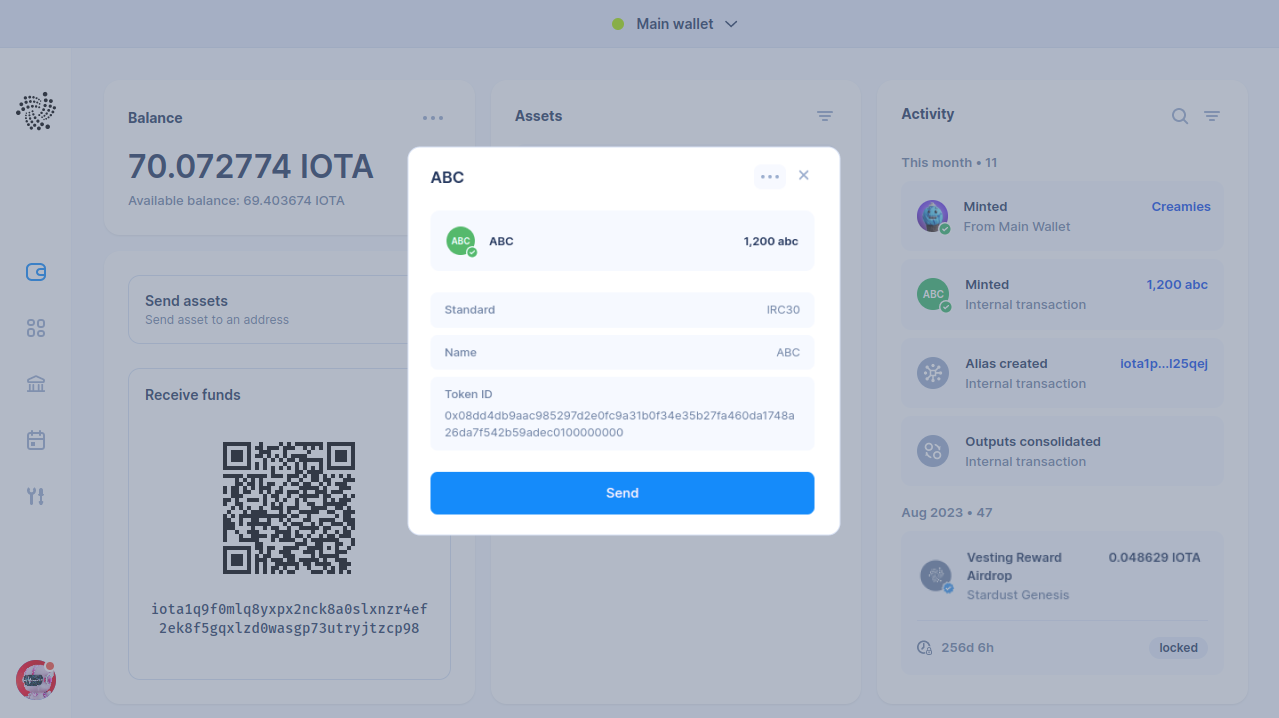
Developer Tools
Convenient tools for developers and creators, such as native token minting.
Ease-of-security
Automated Updated
Automated updates gently remind you of security and feature updates.
Network indicators
Network indicators inform you on the current health of the IOTA network.
Backup and security reminders
Backup and security reminders – make sure you don’t lose anything.
Built with security in mind
Under the hood, the wallet uses [advanced security technology], so that you don’t have to worry about it.
Written in Rust
Rust offers security from the ground up – while maintaining speed, low memory usage and scalability. This allows us to build apps with better performance and higher security.
Secured with Stronghold
Sensitive actions like address generation and transaction signing take place in isolated application memory, keeping the seed away from potential attackers.
Modular design
Firefly separates different functionalities – like seed storage, handling transactions, and cryptography – in crates. A crate groups related functions, so that the functionality is easy to share between multiple projects.
Crypto.rs
Crypto.rs combines all cryptographic algorithms used by many of the projects at IOTA Foundation. It reduces the risk of using unsafe [crypto implementations]. [making it easier to audit, resulting in verifiably safer code.]
Download Firefly
Firefly IOTA
Manage your IOTA assets directly from your computer with both software and hardware wallet support. Earn staking rewards and participate in governance votes.
Firefly Shimmer
Try out new features introduced with Shimmer, such as minting native tokens, setting transaction expiry times, and sending microtransactions.